Mobile App Security Testing
On average, mobile organization users open over 20 applications daily. Speed digital transformation and mobile-first organization processes with mobile app security testing solutions to identify and reduce sophisticated threat vectors.
Get A Demo
Dangers of Insecure Mobile Apps
of all digital traffic & time is spent in mobile vs. web apps
of App Store Apps have Security Flaws that violate OWASP standards
of app store apps leak PII possibly violating CCPA / GDPR
growth in supply chain cyber attacks in the past year
mobile apps and growing across Google Play and Apple App stores
Mobile Threats on the Rise,
Require Automated and Expert
Manual Testing Approaches
Mobile is the enterprise’s largest revenue growth engine but also a growing threat vector highlighting the financial dangers of insecure mobile apps. Statista notes apps will generate nearly $935.2 billion USD with nearly 13.1 billion global mobile devices and connections by 2023. Without automated mobile app testing tools, many apps are dangerously insecure even with widely available, approved for distribution app store availability.
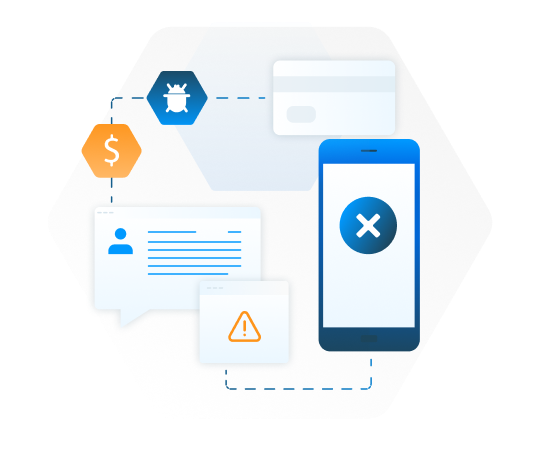
Mobile Apps Present Clear Threat
to Business Data
Mobile AST programs often fail due to poorly defined security requirements and a reliance on legacy web AST tools. The most successful mobile application security testing programs include policies built on standards, developer education and enablement, and integrated automated testing with purpose-built tools. Skyrocketing mobile use for everyday organization processes mandates Mobile AST to reduce costly consequences of data breaches including financial losses, system downtime and brand damage. Without applying security testing best practices, most published mobile applications collect and leak immense PII which can violate CCPA or GDPR.
Mobile App Security Testing
Slows Down Releases
Mobile digital transformation and modern app development practices complicate the process of securing mobile apps as the demand for speed to market can lead to the sacrifice of security measures. Traditional web AST tools are riddled with false positives and manual approaches slam the brakes on agile methodologies. In order to deliver secure mobile apps faster, organizations must utilize automated tools built by mobile experts, integrated directly into development workflows, and configure risk-based policies based on industry best practices from organizations like OWASP.

Fundamental Differences
Between Web and Mobile Apps
Modern mobile threat landscape and application security verification standards include a distinct set of exploitation
vectors. Mobile apps with highly sensitive data require more rigorous security testing in comparison to web applications due to a lack of device-side layered security found behind web firewalls.
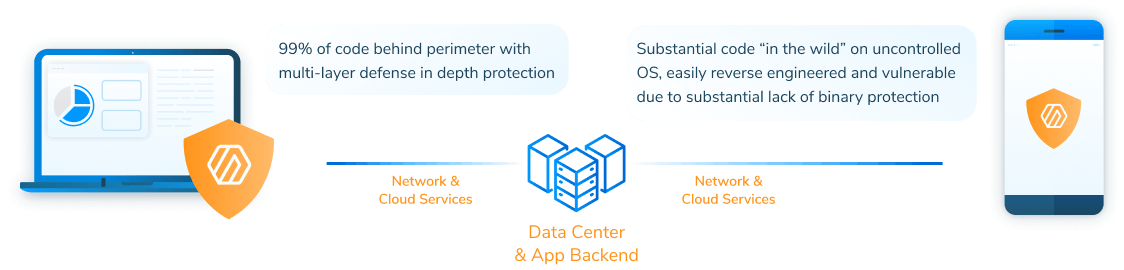
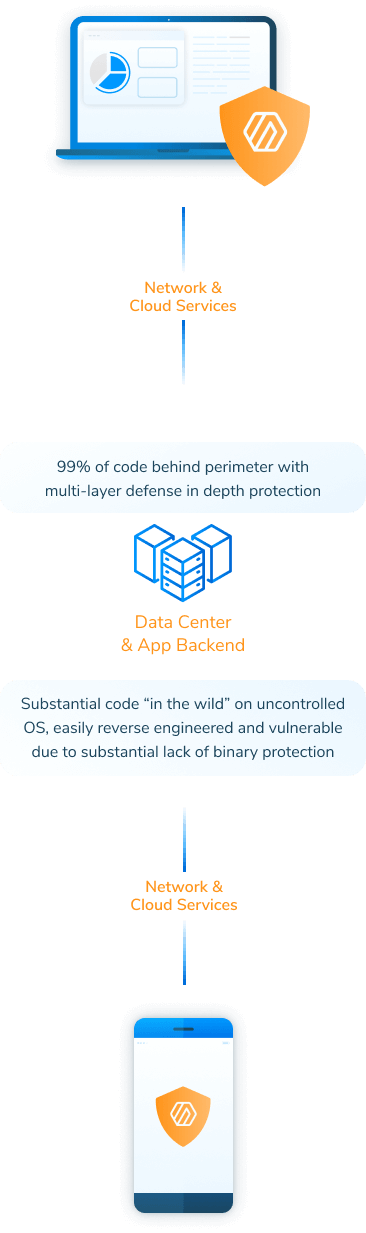
Web App
- Browser inherently isolated from client machine OS and other apps on client
- Majority of executable code resident on a server behind firewall and other layered protection
- Browser securely executed SSL/HTTPS process
- Browser real-time segmentation and control of data from local machine memory and secured files
- Test frameworks securely fed directly into always secure browser environments
Mobile App
- Full operating system underlies the app AND other apps open to interact, inject vulnerabilities, and new attack vectors (e.g. SQL and clients-side interjection)
- Mobile device stores treasure trove of executable app code, IP logic, third party library APIs, data all with weak server-side controls and encryption (e.g. jailbroken devices)
- Development team required to properly code/update all network calls, authentication, and authorization
- Developers require hardened code to handle local memory and files with proper barriers to hacker’s lateral movements
- Hardened iOS and Android OS including encryption, containerization dramatically increases app complexity and unintended data leakage
Best Practices for a Successful Mobile AST Program
Consider the full depth of industry testing resources, developer friendly methods, assets, and accelerators to enable quality mobile applications consistently delivered with quality, rigor, and measurable value across all industries.
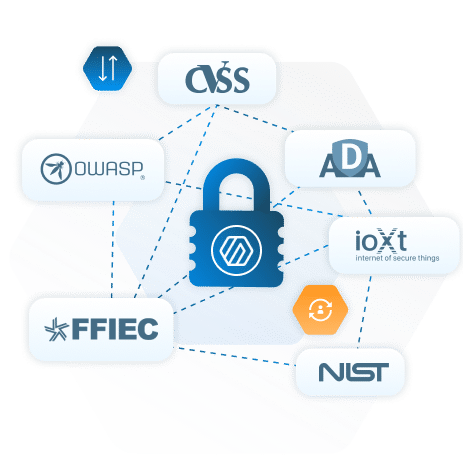
Set Mutually Agreed Policies via Standards
Bridge the gap between mobile app security and development by creating standards-based policies. Tiering policies based on PII sensitivities, app attack surfaces, and risk tolerance help drive secure mobile app development and deployment.
Train AppSec and Dev Teams
Upskill mobile app security and development teams by leveraging NowSecure Academy free resources. Shift left as developers write secure code from the start and deliver mobile apps faster and more securely. Shift right as mobile app security analysts learn best practices for thoroughly assessing mobile apps.
Test Continuously for Fast Feedback Loops
Integrate and automate assessments to run in the SDLC on every code commit, pull request, or application build. Quickly identify new vulnerabilities introduced to the codebase and fix them to continuously improve the security posture of the mobile app.
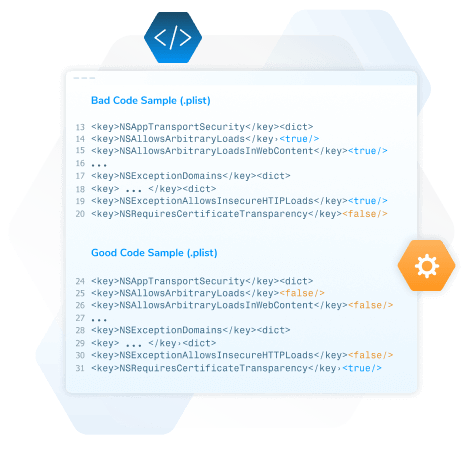
Embed Remediation Assistance and Resources
Make findings easy to remediate by providing developers with embedded replication instructions, sample code blocks and Apple and Google documentation. Provide these resources directly in the CI/CD pipeline via integration.
Pen Test for High Risk & Complex Scenarios
Utilize periodic expert mobile app penetration tests or Pen Testing as a Service (PTaaS) in addition to automated tests to build a threat model of mobile app security risks, ensure coverage of complex workflows and requirements, and verify fixes and mitigations.
Continuously Monitor Production & App Stores
Assess security risks coming from published, publicly available mobile apps introduced to corporate environments. Integrate mobile app security data into Mobile Device Management solutions to ensure an insecure mobile app bought or downloaded does not introduce new attack vectors.

CASE STUDY

Integrating automated scanning into the CI/CD pipeline has been transformative for us.
Lead Mobile Application Security Engineer
CASE STUDY

If the device stops working, the patient stops working.
Business Unit Director of Product Security
CASE STUDY

NowSecure’s role in reducing vulnerabilities and supporting our application security program has been instrumental in achieving our security goals.
Senior Security Analyst
CASE STUDY
We reached out to NowSecure and were pleased that they rapidly responded in 24 hours to test our mobile app so we could speed it to market from start to finish in just a few weeks.”
One Platform for Mobile App Risk Management (MARM)
NowSecure MARM is a SaaS solution for identifying, prioritizing and remediating mobile app risk for the apps you build and the thousands of third-party apps in your environment.
What Makes NowSecure Different?
- Single platform for security, privacy, safety and compliance risk management
- Dynamic runtime testing reveals data leaks leading to enhanced data privacy protection
- Automation from testing through remediation and reporting
- Apps you build and third-party apps
- Discover risks in third-party SDKs and endpoints
- Test apps against OWASP Standards for mobile app security

Learn How to Grow
Your Mobile AppSec Program
Get Mobile Application Risk Management. Test don’t guess.
See the NowSecure Platform in action
Mobile App Security Testing FAQs
What is mobile app security and why is it important to test?
Mobile app security protects applications, APIs, and connected services from vulnerabilities that can expose sensitive data, compromise user privacy, or enable fraud.
At NowSecure, we believe mobile apps operate in highly dynamic environments where threats evolve continuously and public app store reviews alone are not sufficient to guarantee safety. Security testing is essential because mobile apps often handle credentials, financial information, healthcare data, and enterprise access.
Without comprehensive testing, organizations risk data breaches, compliance violations, brand damage, and operational disruption. Effective mobile app security testing identifies weaknesses in code, APIs, encryption, authentication, and third-party SDKs before attackers exploit them. Continuous testing also helps organizations meet OWASP MASVS, regulatory, and enterprise risk management requirements while ensuring secure app releases across both iOS and Android environments.
What are the most common vulnerabilities or risks in mobile apps?
The most common mobile app risks include insecure data storage, weak authentication, exposed APIs, improper encryption, hardcoded secrets, insecure network communications, and vulnerable third-party SDKs.
At NowSecure, we also frequently identify risks related to excessive permissions, insecure session handling, code tampering, jailbreak or root detection failures, and privacy leakage through analytics or advertising libraries. API data exposure remains a major concern because mobile apps constantly exchange sensitive information with backend systems.
Many apps also fail to properly protect personally identifiable information (PII) and enterprise credentials. Public app stores cannot reliably detect these issues, especially runtime vulnerabilities and hidden behaviors. Attackers exploit these weaknesses to steal data, hijack accounts, distribute malware, or compromise enterprise systems, making continuous security validation critical for both consumer and enterprise mobile applications.
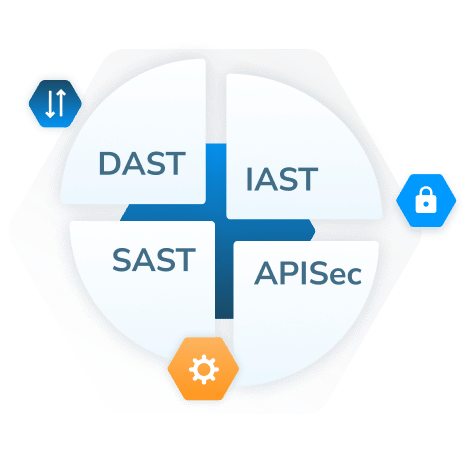
What methodologies and tools should be used for mobile app security testing?
NowSecure recommends a layered testing methodology that combines automated static analysis (SAST), dynamic analysis (DAST), interactive testing, API security testing, and expert manual penetration testing.
Static analysis identifies insecure code patterns, secrets, and misconfigurations early in development, while dynamic testing evaluates runtime behavior, encryption, network traffic, and data handling during app execution. API testing is essential because mobile apps depend heavily on backend services and cloud integrations.
Manual testing complements automation by uncovering complex business logic flaws and sophisticated attack paths that tools alone may miss. Effective mobile app security programs should also validate apps against OWASP MASVS standards and continuously monitor third-party SDKs and supply chain risks. Integrated DevSecOps tooling enables organizations to automate testing within CI/CD pipelines while maintaining visibility across both iOS and Android applications.
When and how often should mobile app security testing be performed?
Mobile app security testing should begin early in development and continue throughout the entire software lifecycle.
At NowSecure, we recommend integrating automated security testing into every build and release cycle so vulnerabilities are identified before production deployment. Testing should occur during development, pre-release validation, major feature updates, SDK changes, backend API modifications, and after operating system updates that may introduce new risks.
Continuous testing is especially important because mobile threats evolve rapidly and third-party components frequently change. Organizations should also conduct periodic manual penetration testing to validate defenses against advanced attack scenarios.
High-risk applications handling financial, healthcare, or enterprise data may require ongoing monitoring and more frequent assessments to maintain compliance and reduce exposure. Continuous mobile security testing enables organizations to release apps faster while maintaining stronger security and risk management.
What scope should the mobile app security testing cover?
Mobile app security testing should cover the entire mobile ecosystem, including the mobile application, APIs, backend infrastructure, third-party SDKs, authentication systems, cloud services, and data flows.
At NowSecure, we emphasize that testing only the mobile binary is insufficient because many vulnerabilities originate from APIs, insecure integrations, or external components. A complete testing scope should evaluate source code, runtime behavior, encryption, network communications, data storage, permissions, authentication, session management, and jailbreak or root protections.
Organizations should also assess software supply chain risks from embedded SDKs, analytics libraries, and advertising frameworks. Testing should include both iOS and Android platforms as well as variations across devices and operating system versions. Comprehensive coverage ensures security gaps are identified across the full attack surface instead of isolated application components.
What are the core testing methods of mobile app security testing?
The core methods of mobile app security testing include static application security testing (SAST), dynamic application security testing (DAST), interactive testing, API testing, and manual penetration testing.
NowSecure uses these complementary approaches to provide broad and accurate visibility into mobile risk. Static testing analyzes application code and binaries to identify insecure coding practices, secrets, and configuration weaknesses.
- Dynamic testing evaluates app behavior during runtime, including network traffic, encryption, authentication, and data leakage.
- Interactive testing combines runtime analysis with instrumentation for deeper behavioral insight.
- API testing validates backend communications and identifies insecure endpoints or exposed data.
- Manual penetration testing remains essential for uncovering business logic flaws, chaining vulnerabilities, and validating exploitability.
Combining these testing methods provides stronger coverage for modern iOS and Android applications than relying on any single technique alone.
What are the best practices of mobile app security testing?
Best practices for mobile app security testing include shifting security left in development, automating testing within CI/CD pipelines, validating apps against OWASP MASVS standards, and continuously monitoring production risks.
At NowSecure, we recommend combining automated and manual testing methods to maximize vulnerability coverage and reduce blind spots. Organizations should test both iOS and Android apps regularly, including APIs, backend services, and third-party SDKs.
Developers should remediate vulnerabilities quickly using actionable findings with minimal false positives. Security testing should also verify encryption, authentication, data privacy, certificate handling, and runtime protections. Continuous testing after updates, SDK changes, or new releases is critical because mobile ecosystems evolve rapidly. Integrating security into DevSecOps workflows helps teams maintain release velocity while improving risk management, compliance, and overall mobile application resilience.
How do I get a NowSecure demo for mobile app security testing?
During a demo, NowSecure experts typically showcase automated vulnerability detection, OWASP MASVS coverage, API and SDK analysis, CI/CD integration capabilities, and reporting workflows designed for developers, security teams, and compliance stakeholders.
How do we reduce false positives in mobile app security testing for developers?
Reducing false positives requires accurate analysis, contextual validation, and developer-focused reporting.
At NowSecure, we minimize false positives by combining static, dynamic, and runtime testing techniques to validate whether vulnerabilities are actually exploitable. Correlating findings across multiple testing methods helps eliminate noisy or duplicate alerts that slow remediation efforts.
Automated results should also map directly to OWASP MASVS controls and provide actionable remediation guidance so developers can quickly prioritize real risks. Integrating testing into CI/CD pipelines enables earlier validation and faster feedback during development.
Manual verification of critical findings further improves accuracy for complex issues. Organizations benefit most when security tools provide clear evidence, reproducible results, and contextual risk scoring rather than overwhelming developers with unactionable alerts that reduce trust in the testing process.
Can NowSecure integrate mobile app security testing into GitHub Actions, GitLab, or Azure DevOps?
Yes. NowSecure supports integration with modern DevSecOps and CI/CD platforms including GitHub Actions, GitLab CI/CD, Azure DevOps, Jenkins, and other enterprise automation environments.
These integrations allow organizations to automate mobile app security testing directly within development workflows for both iOS and Android applications. By embedding security checks into build and release pipelines, teams can identify vulnerabilities earlier, enforce security policies, and prevent risky applications from progressing to production.
Automated integrations also help developers receive rapid feedback with actionable remediation guidance while maintaining release velocity. NowSecure’s CI/CD support enables continuous testing for APIs, binaries, SDKs, and runtime behaviors while aligning with OWASP MASVS and enterprise compliance requirements. This approach helps organizations scale mobile security testing consistently across agile development environments.
What is the best way to add mobile app security testing to CI/CD without slowing releases?
The best approach is to automate security testing early in the development lifecycle using fast, policy-driven workflows integrated directly into CI/CD pipelines.
At NowSecure, we recommend combining lightweight automated scans during development with deeper runtime and manual testing before major releases. Risk-based testing policies help teams prioritize critical vulnerabilities while reducing unnecessary build failures.
Incremental testing, parallel execution, and automated remediation guidance also minimize disruption to developer productivity. Integrating security into GitHub Actions, GitLab, Azure DevOps, or Jenkins allows teams to continuously validate mobile apps without adding manual bottlenecks.
Continuous testing of binaries, APIs, SDKs, and runtime behaviors ensures vulnerabilities are identified quickly while preserving release speed. This DevSecOps approach helps organizations improve mobile security posture without sacrificing agile delivery timelines.
What are the best practices for selecting a mobile app security testing vendor for enterprise apps?
Organizations should select a vendor that provides comprehensive coverage across iOS, Android, APIs, backend services, and third-party SDKs while supporting both automated and manual testing methodologies.
At NowSecure, we believe enterprise mobile security testing solutions should align with OWASP MASVS standards, integrate seamlessly into CI/CD workflows, and minimize false positives with validated findings. Vendors should demonstrate strong runtime analysis capabilities, accurate vulnerability detection, scalable automation, and actionable remediation guidance for developers.
Enterprises should also evaluate support for DevSecOps integrations, compliance reporting, privacy validation, and software supply chain risk analysis. Transparent reporting, enterprise scalability, and continuous testing capabilities are essential for modern mobile environments. The ideal vendor enables organizations to manage mobile risk proactively while accelerating secure application delivery across complex enterprise ecosystems.
Which mobile app security testing methods should we use together: static, dynamic, interactive, API, or manual testing?
NowSecure recommends using static, dynamic, interactive, API, and manual testing together because each method identifies different categories of risk.
- Static testing detects insecure coding practices, secrets, and configuration issues early in development.
- Dynamic testing evaluates runtime behavior such as encryption, authentication, and network communications during app execution.
- Interactive testing provides deeper runtime visibility by instrumenting applications while they operate.
- API testing is critical because mobile apps depend heavily on backend services that may expose sensitive data or weak authentication controls.
- Manual penetration testing complements automation by uncovering business logic flaws and sophisticated attack paths that tools alone may miss.
Combining these methodologies provides stronger coverage for OWASP MASVS requirements, insecure storage issues, API data leaks, and complex vulnerabilities across both iOS and Android applications.
What should a mobile app security testing scope include for the app, APIs, backend services, and third-party SDKs?
A comprehensive mobile app security testing scope should include the mobile application itself, backend APIs, authentication systems, cloud infrastructure, third-party SDKs, and all associated data flows.
At NowSecure, we recommend evaluating source code, binaries, runtime behaviors, encryption, permissions, session management, and local data storage across both iOS and Android apps. API testing should validate authentication, authorization, rate limiting, sensitive data exposure, and transport security.
Backend assessments should examine cloud configurations, access controls, and server-side vulnerabilities. Third-party SDK analysis is essential because embedded libraries can introduce hidden privacy, compliance, or malware risks. Organizations should also assess software supply chain exposure, insecure communications, and privacy leakage.
Full-scope testing ensures vulnerabilities are identified across the entire mobile ecosystem rather than isolated application components.
Which mobile app security testing methodologies and tools give the best coverage for iOS and Android apps?
The best coverage for iOS and Android applications comes from combining automated static analysis, dynamic runtime testing, API security testing, interactive analysis, and expert manual penetration testing.
At NowSecure, we use layered methodologies because no single testing technique can identify every mobile risk. Static analysis identifies insecure code, secrets, and configuration weaknesses, while dynamic testing evaluates runtime behaviors such as encryption, authentication, and data leakage. API testing validates the security of backend communications and cloud integrations. Interactive testing improves visibility into app behavior during execution, and manual testing uncovers advanced attack paths and business logic flaws.
Effective tools should support OWASP MASVS validation, DevSecOps integration, third-party SDK analysis, and continuous testing workflows to deliver comprehensive mobile security coverage across rapidly evolving mobile ecosystems.
Which mobile app security testing tools are best at finding OWASP MASVS issues, insecure storage, and API data leaks?
The most effective mobile app security testing tools combine static, dynamic, interactive, and API testing capabilities to identify OWASP MASVS violations, insecure storage practices, and API data leaks across iOS and Android applications.
At NowSecure, we emphasize runtime analysis because many mobile vulnerabilities only appear during application execution, including insecure data handling, weak encryption, and exposed network traffic.
Strong tools should validate compliance with OWASP MASVS controls, detect hardcoded secrets, analyze third-party SDK behavior, and inspect API communications for sensitive data exposure. API testing capabilities are especially important because backend services often expose credentials or personal information unintentionally.
The best platforms also reduce false positives, integrate into CI/CD pipelines, provide actionable remediation guidance, and support continuous testing workflows that help organizations scale secure mobile application development efficiently.